 Cyber security is a scary topic. I’d bet many medical technology makers feel unfamiliar with the terminology and would rather not discuss the details. But the reality of hacking is forcing the issue.
Cyber security is a scary topic. I’d bet many medical technology makers feel unfamiliar with the terminology and would rather not discuss the details. But the reality of hacking is forcing the issue.
A few weeks ago, I attended the International Stroke Conference. During my time at the event, I wandered the expo booths and struck up a conversation with a telehealth service provider. To be fair, this person was not an IT expert, but he glossed over my serious question about how the company was protecting itself and the data that’s uploaded via its moving camera system.
What he essentially said was that the company follows the security protocols and they are in compliance. This conversation is emblematic of the feedback I’ve been getting for the past few months. At nearly every level, medical device suppliers, OEMs, and hospitals are not talking about security. We are waving it away.
And if OEMs aren’t talking about it, it means clients aren’t asking. And if no one is asking, it means companies probably aren’t doing the best job ensuring that they’re protected.
Looking at some data that’s come out in the last few weeks, this lack of initiative grows even scarier:
- A report from the Institute for Critical Infrastructure Technology finds that recent cybersecurity guidance for device makers from the FDA falls way short.
- Redspin’s Breach Report 2015: Protected Health Information (PHI) concluded that hacking attacks factored in 9 of the 10 largest breach incidents of the year – incidents which led to the compromise of 98.1% of all patient records breached in 2015.
- The same report said that “phishing” – tricking healthcare employees into disclosing their login ID’s and passwords through fraudulent emails or other methods – played a role in many of the 2015 hacking attacks.
- On Feb. 18, Hollywood Presbyterian Medical Center paid a $17,000 ransom in bitcoin to a hacker who seized control of the hospital’s computer systems including blocking access to patient records.
These troubling trends are being considered by a subset of the industry that does want to discuss the problem: Embedded software security providers.
One of the challenges, says Battelle’s Stephanie Preston, is legacy products. Preston is an embedded systems engineer and certified ethical hacker. She says that medical devices are a unique challenge due to their long development life cycles – ranging anywhere from 18 months to 10 years – and their long deployment life. “I’ve heard rumors of devices as old as 20 years still operating in hospitals.”
Preston says in the immediate term, “manufacturers need to take a look at their currently fielded devices to determine the security situation they’re in.” She advises that OEMs perform vulnerability assessments, or conduct penetration tests on devices that are in care situations. Those results should help OEMs prioritize and develop a strategy for securing the devices.
“The long game is for manufacturers to adopt secure design practices, and incorporate vulnerability assessments and testing as a routine part of the development lifecycles,” says Preston.
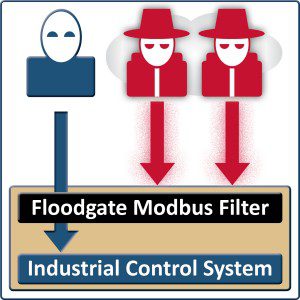 Icon Lab president Alan Grau has an approach that could help. Icon just released its Floodgate Modbus Protocol Filtering product. This extension to Icon Labs’ Floodgate Security Framework adds critical protection capabilities for Industrial IoT and RTOS-based devices. The group partnered with Renesas Industrial Automation to demonstrate the process.
Icon Lab president Alan Grau has an approach that could help. Icon just released its Floodgate Modbus Protocol Filtering product. This extension to Icon Labs’ Floodgate Security Framework adds critical protection capabilities for Industrial IoT and RTOS-based devices. The group partnered with Renesas Industrial Automation to demonstrate the process.
Icon is betting that its embedded system will provide a deeper level of protection for medical device technologies.
“This is not just hardware in front of the device,” says Grau. “Our customers really want to make sure they are providing secure products to the market.”
He also noted that 50% of attacks come from internal sources and are not all malicious in intent. “If a user does something inadvertently, e.g., changes a setting in a way that causes the system to react, you can still be protected if your illegal actions are protected with embedded security in the device.
There’s a saying among security experts, he says: “There are two kinds of companies, those who have been hacked, and those who don’t know they’ve been hacked.” Grau says we shouldn’t expect medical product companies or hospitals to be any different.




