The following is the second part of a series by Mike Nelson, DigiCert & Dale Nordenberg, MDISS. Please refer to Public Key Infrastructure: A Trusted Security Solution for Connected Medical Devices (Part 1).
PKI Deployment Considerations
Deploying, managing, and maintaining an enterprise-level PKI security solution can be a complicated task. Organizations that seek to implement and maintain an on-premise or in- house PKI security solution should consider the following challenges and complications before making the decision to act as their own internal CA.
PKI EXPERTISE
Understanding PKI is complex and typically isn’t an IoT manufacturer’s full-time role. PKI expertise is needed to help clarify and comprehend data security requirements, such as FIPS 140-2 level 2, ECDHE cipher suites, PKCS #11 cryptographic interfaces, root ubiquity compliance, and X.509 OIDs.
CRYPTOGRAPHIC AGILITY
Cryptography is constantly changing. What was considered completely secure and safe to use three or four years ago is now deprecated. There are aspects of certificates which may require an even quicker turn-around of switching substantial infrastructure to new or different cryptographic properties.
Most PKI implementations are built to enable IoT projects to take advantage of updates to curves, algorithms, and hashes as these technological capabilities become available. When vulnerabilities are found or deprecation occurs, the CA must have the ability to immediately switch to a secure alternative. This advantage is typically not found with new security standards or security alternatives being developed.
SYSTEM AVAILABILITY
Core IoT services require exceptional uptime and availability. When dealing with globally disparate certificate provisioning, verification, and revocation, deploying a brand new infrastructure to support the many needs of such systems is not logistically feasible for most organizations and is almost never economically feasible when compared to using systems already in place.
INFRASTRUCTURE SCALABILITY
Certificates are used to secure sensitive and valuable information. Investing in servers and infrastructure needed to handle mass issuance, reissuance, and/or revocation events is necessary to ensure integrity of the PKI systems. Those events are rare, but the cost involved in such an investment can be large, especially when dealing with tens of thousands or hundreds of millions of certificates.
SECURITY
The security requirements of running a CA are substantial. Your Root CA needs to be secured to the absolute highest level, which requires investment in hardware, CA software, infrastructure, PKI architects, consulting services, and training.
COST
While using an internal or private CA might seem ideal and even a more cost-effective solution at first, it is important to understand the underlying costs of hosting, deploying, and maintaining on-going CA infrastructure systems. Hosted CA infrastructure with a commercial Certificate Authority can deliver competitive pricing for critical services which can automatically scale with certificate issuance. This allows your investment to start at an already financially viable position and grow to more affordable levels as your IoT certificate issuance increases.
LIABILITY
If an internal CA is compromised and enables access to privileged data, the damage to a company’s reputation is often detrimental, not to mention the resulting monetary loss can be significant. Separating management of some parts of an organization’s security solution can not only increase the overall security of that solution, but also help to minimize damages in worst-case scenarios.
COMPLIANCE AND DATA CONTROL
Hosted, cloud-based PKI services also come with their own set of internal compliance and data control concerns, especially for devices or systems dealing with medical or patient data. Effectively implementing and managing a PKI solution requires adherence to PKI standards, industry requirements, potential government mandates, data storage requirements, certificate management policies, training personnel, and data recovery policies. Additional considerations should be made for often hidden requirements of security deployments.
PUBLIC TRUST
While private PKI may be used by some IoT providers, having the ability to also flexibly issue publicly trusted certificates is incredibly valuable. An internal CA may never be able to be used in a way that is trusted automatically by external services or relying parties, leading to certificate-related errors for users engaging with IoT devices or with devices attempting to establish connections with back-end systems and services.
PKI Uses for Connected Medical Devices
Before digital certificates are deployed to a medical device, the right infrastructure for overseeing certificates needs to be
in place. A certificate management platform that streamlines critical aspects of a certificate lifecycle (provision, issue, renew, revoke) allows manufacturers to be dedicated to security without additional hassle or error. Platforms should be flexible, reliable, and enable the manufacturer to scale.
IoT manufacturers will benefit from using a platform that allows them to:
- Provision, issue, renew, and revoke certificates
- Create custom certificate profiles
- Deploy a high volume of certificates
- Scan and remediate TLS vulnerabilities
- Review analytics and reports
- Securely store and manage certificate keys
Once a manufacturer has a certificate management platform in place, they can then deploy certificates for authentication, encryption, and signing services.
AUTHENTICATION SERVICES
PKI enables the safe authentication of users, systems, and devices without the need for tokens, password policies, or other cumbersome user-initiated factors. With PKI, IoT solutions can enable direct authentication across systems. PKI also offers the highest levels of identify assurance, providing a measure of confidence that the entities at both ends of a data transaction or authentication event are who they claim to be. Effective identity verification is a fundamental element for effective security and connected device trust. PKI certificates provide evidence that the identity of organizations, domains, and devices was properly established because certificates cryptographically bind public keys to such identities.
ENCRYPTION SERVICES
PKI affords the capability to address the security needs of data in transit. While not vulnerable to common brute- force or user-deception attacks, PKI facilitates the secure transmission of sensitive information. When a connected device transmits or receives sensitive personal health information (PHI) over the Internet, the data must be encrypted. Digital certificates can be used to ensure the highest level of HIPAA-compliant encryption is used to secure this data.
SIGNING SERVICES
Signing services ensure data and device integrity by making sure any messages sent to a device from sensors or other intelligent systems are not intercepted and remain unaltered. PKI also facilitates the verification of availability and access for protocol configurations, applications, or interaction with data stored in the device. This ensures the complete coverage of data and system confidentiality, integrity, and availability.
PKI can be used to provide secure signing services in the following ways:
- Data Integrity: Certificates can be used to ensure data being sent to and from a connected device has not been intercepted and modified in transition.
- Secure Device Boot: When a device is started, certificates are used to ensure the configuration settings, software, firmware, or other components of the device have not been modified from the desired settings.
- Firmware Authentication: When a firmware update is sent to a connected device, certificates can be used to ensure the update is coming from a trusted source and signed by a trusted and/or pinned certificate.
- Software Code Signing: When manufacturers put software on a connected device, certificates can be used to sign the code, ensuring it hasn’t been modified.
PKI Use Case: Wireless Infusion Pumps & Pump Servers
This use case shows how PKI can be used with wireless infusion pumps and servers to securely authenticate and encrypt any communication coming to and from the
devices. The workflow of a wireless infusion pump includes connecting to a wireless pump server to receive drug dosage information. The pump server then connects with multiple outside sources such as the electronic medical record (EMR) system, e-prescribing system, and even pharmacies to send and receive drug data. This use case will focus on authentication between the pump and the pump server.
Similar authentication and encryption should also be in place for the pump server and other outside connections.
Each of these connections requires a method to identify one another and a securely encrypted transfer of data that can be checked for authenticity. Without the ability to identify one another and properly encrypt the data, the wireless infusion pumps could receive data from non-trusted sources that contain malware or counterfeit drug dosage information. The data being sent could also be intercepted by a perpetrator, the drug dosage amounts could be manipulated to lethal levels, and the counterfeit drug data could arrive at the wireless pump and be administered to the patient.
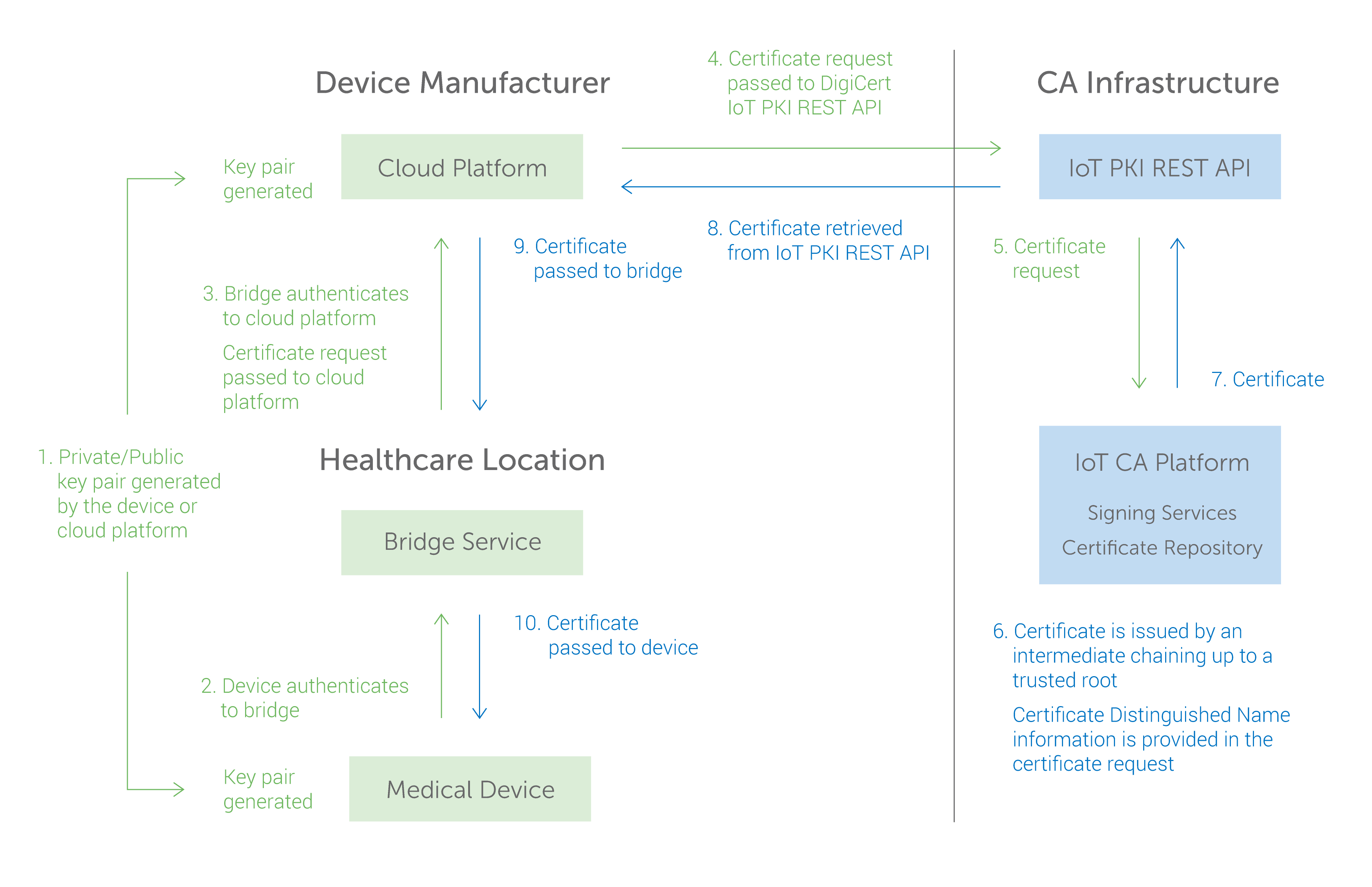
PUBLIC/PRIVATE KEY CREATION AND PROVISIONING
Mutual authentication using public/private key pairs must be performed in order to secure the different connection points between wireless infusion pumps and pump servers. To do this, a public/private key pair is created based on strong cryptographic technology that cannot be counterfeited. A CA then combines the public key with the information used to uniquely identify the private key (such as the serial number of the pump) and signs the resulting certificate file. When this is complete the private key and certificate are imported to each pump and server through a secure process. (See graphic.) Once the private key is contained on the device it cannot be tampered with or exported from the device. The private key and certificate are unique for each device.
AUTHENTICATION
Mutual authentication using public/private key pairs is performed each time the wireless infusion pump connects with the pump server. Each time a connection is initiated a secure “handshake” takes place, validating both the server and pump as trusted sources. The server uses its private key to sign an authentication then passes the signed authentication and its certificate to the pump. The pump inspects the certificate provided by the server to ensure it can be trusted. The pump uses its private key to sign an authentication then passes the signed authentication and its certificate to the server. The server inspects the certificate provided by the pump to ensure it can be trusted. During this process if the certificate used by the pump and server are trusted, the session continues, otherwise the connection is terminated.
ENCRYPTION
Once the pump and server have completed their mutual authentication, the server continues the process of establishing an encrypted session with the pump. An ephemeral symmetric session key is generated and shared between the pump and the server. The session key is used to encrypt any data transferred between the pump and the server. A new session key is created each time the pump makes a connection with the server. The encrypted session ensures the integrity of the data in transit between the pump and server.
SIGNING
In this use case, the manufacturer’s process passes the pump configuration parameters to the pump using a signed configuration file. The pump configuration file must be signed by the server and the pump must check the signature of the file before applying the configuration which will set the parameters it uses to deliver substances to patients.
The proper use and configuration of public/private key pairs have shown to reliably prove authenticity and prevent the introduction of counterfeit devices, as well as protect data sent between pumps and servers using encryption.
(Credit: Mike Nelson, DigiCert & Dale Nordenberg, MDISS)
Summary
PKI is the foundation for securing the growing number of connected devices within the healthcare industry. Its existing technologies, when correctly implemented, can mitigate the security risks associated with large-scale device deployments.
IoT ecosystems that use PKI are able to properly apply encryption, authentication, and signing services. Additionally, a PKI-based IoT security solution ensures strong identity and message integrity for data exchange between systems, devices, applications, and users.
To achieve a comprehensive PKI solution, IoT providers should consider the hardware, software, people, policies, and procedures needed to create, manage, distribute, use, store, and revoke digital certificates, as well as manage the encryption process. Using a high-volume issuance platform complements PKI and provides the scalability and flexibility that many IoT manufacturers require.
As technical innovation continues to push the market forward, organizations are adopting this scalable and flexible solution to deliver the highest levels of security for their connected devices.